Information Collected by Dharmesh Prajapati
The Pakistan-linked threat group Transparent Tribe has started using artificial intelligence powered coding tools to develop and deploy a wide range of malware implants against its targets.
According to new research by Bitdefender, the attackers are producing a large number of moderately built malware samples using less common programming languages such as Nim, Zig, and Crystal. These implants also rely on trusted platforms like Slack, Discord, Supabase, and Google Sheets for communication, helping them remain unnoticed.
Security researchers Radu Tudorica, Adrian Schipor, Victor Vrabie, Marius Baciu, and Martin Zugec explained that this campaign does not represent a major advancement in technical sophistication. Instead, it reflects a shift toward AI-assisted malware production at scale, allowing attackers to overwhelm target systems with numerous disposable and multilingual binaries.
This emerging technique, often referred to as vibe-coded malware or “vibeware,” aims to make detection more difficult. Bitdefender describes this strategy as Distributed Denial of Detection (DDoD). Rather than creating highly sophisticated malware, attackers generate a flood of disposable programs written in different languages and using varied communication protocols to confuse security systems.
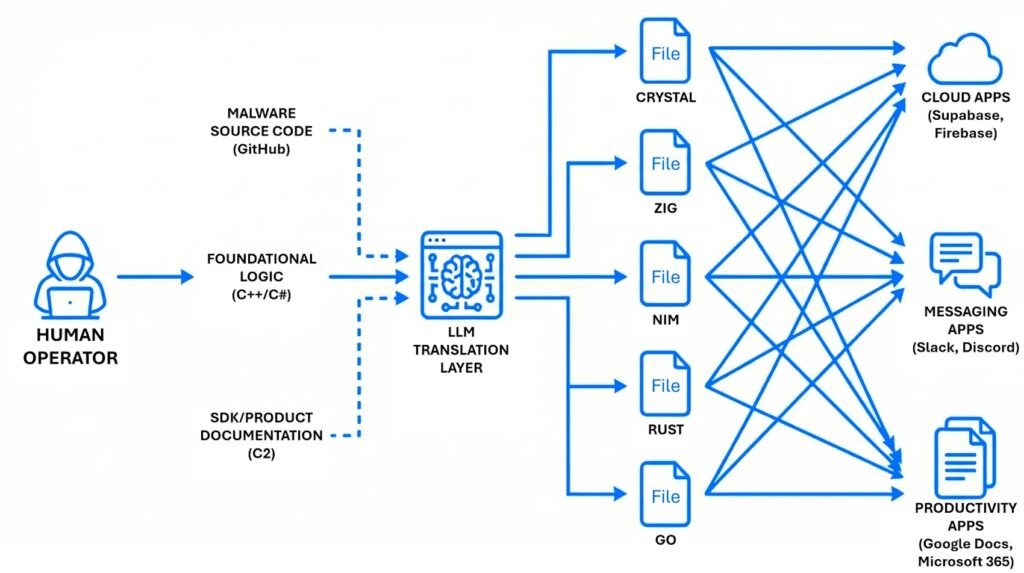
Large language models (LLMs) are helping cybercriminals significantly in this process. These AI systems reduce the technical expertise needed to conduct cyberattacks by allowing threat actors to generate working code in unfamiliar programming languages or convert existing code from common languages.
Recent attacks linked to this campaign have primarily targeted the Indian government and several Indian embassies abroad. The group, also known as APT36, reportedly used LinkedIn to identify and track high-value targets. Some attacks have also been directed at the Afghan government and certain private organizations, although to a lesser degree.
The infection process typically begins with phishing emails containing Windows shortcut files (LNK) hidden inside ZIP archives or ISO files. In some cases, victims are sent PDF documents with a “Download Document” button, which redirects them to a malicious website that downloads the same archive files.
Once executed, the LNK file launches PowerShell scripts directly in memory, which then download and run the primary backdoor and enable further malicious activity. Attackers also deploy well-known adversary simulation tools such as Cobalt Strike and Havoc, indicating a hybrid attack strategy designed for greater reliability.
Several additional tools have been observed in these operations:
- Warcode – A custom shellcode loader written in Crystal that loads a Havoc agent directly into memory.
- NimShellcodeLoader – An experimental version of Warcode used to deploy a Cobalt Strike beacon.
- CreepDropper – A .NET malware responsible for delivering other payloads, including SHEETCREEP, a Go-based information stealer using Microsoft Graph API for command and control, and MAILCREEP, a C# backdoor that uses Google Sheets for communication.
- SupaServ – A Rust-based backdoor that communicates through the Supabase platform with Firebase as a backup channel. The presence of Unicode emojis suggests it may have been developed using AI tools.
- LuminousStealer – Another Rust-based infostealer that uses Firebase and Google Drive to exfiltrate files with specific extensions such as documents, images, spreadsheets, and archives.
- CrystalShell – A Crystal-based backdoor capable of targeting Windows, Linux, and macOS systems. It uses Discord channels for command-and-control and can execute commands and collect system information. Some versions use Slack instead.
- ZigShell – A Zig-based variant of CrystalShell that primarily uses Slack for command-and-control and can transfer files.
- CrystalFile – A simple command interpreter written in Crystal that monitors a specific file path and executes commands using Windows command prompt.
- LuminousCookies – A Rust-based injector designed to steal cookies, passwords, and payment data from Chromium-based browsers by bypassing encryption protections.
- BackupSpy – A Rust tool that monitors the local file system and external drives for valuable data.
- ZigLoader – A loader written in Zig that decrypts and executes shellcode directly in memory.
- Gate Sentinel Beacon – A modified version of the open-source GateSentinel command-and-control framework.
Despite the increased volume of malware, Bitdefender notes that the group’s move toward vibeware actually represents a decline in technical quality. AI-generated malware often contains unstable code and logical errors. Additionally, the attackers appear to be focusing mainly on bypassing signature-based detection, even though modern security systems rely on more advanced detection techniques.
However, researchers warn that the real danger lies in the large-scale production of malware enabled by AI, which allows threat actors to launch widespread campaigns quickly and with minimal effort.
According to Bitdefender, this campaign highlights the merging of two growing trends: the use of uncommon programming languages and the abuse of legitimate cloud services to conceal malicious activity within normal network traffic. Together, these tactics enable even average-quality malware to achieve significant operational success by overwhelming traditional security monitoring systems.
Editorial Note
This article is based on findings from cybersecurity research published by Bitdefender regarding the activities of the Pakistan-linked hacking group Transparent Tribe (APT36). The report highlights the growing use of artificial intelligence and large language models in malware development, allowing threat actors to generate large volumes of malicious code quickly. The content has been adapted and summarized for informational and public awareness purposes, particularly in the context of cyber threats targeting Indian government entities and institutions.
